Raspberry PI as VPN endpoint for Sophos XG Firewall
I have been running Raspberry Pi device on my summer cabin as an MotionEye server for multiple security cameras. From time to time I need to make some changes to settings on these cameras but I do not want to open remove management over public internet or use provided cloud services.
Instead I decided to set up strongSwan IPsec server on the Raspberry Pi and create Lan2Lan tunnel between Raspberry Pi at cabin and Sophos XG Firewall at home.
First lets install necessary packages on Raspberry Pi.
sudo apt-get install strongswan libcharon-extra-pluginsEdit /etc/strongswan.conf configuration-file and add your preferred DNS servers. I use my favorite ones from quad9.net
charon {
load_modular = yes
dns1=9.9.9.9
dns2=149.112.112.112
plugins {
include strongswan.d/charon/*.conf
}
}
include strongswan.d/*.confNext edit /etc/ipsec.conf config-file and define internal networks and VPN endpoints. Rightsubnet is your network on Sophos XG Firewall side. Leftsubnet is network where Raspberry Pi is located.
config setup
protostack=netkey
keep_alive=30
conn RPI-HOME
type=tunnel
authby=secret
leftsubnet=192.168.1.0/24
left=192.168.1.3
right=fw.example.com
rightsubnet=192.168.2.0/24
rightid=fw.example.com
keyexchange=ikev2
authby=secret
ike=aes128-sha256-modp2048
ikelifetime=86400s
phase2=esp
phase2alg=aes128-sha256-modp2048
keylife=3600s
auto=start
keyingtries=3
lifetime=1hEdit /etc/ipsec.secrets and add pre-shared key being used for encryption. I use key that has 64 characters.
fw.example.com : PSK "longandstrongpasswordgoeshere"Next we need to allow forwarding on Raspberry Pi so that it can pass traffic coming from VPN-tunnel. Edit /etc/sysctl.conf config-file and add following line in the end of the file. After saving the file run sudo sysctl -p to reload the configuration.
net.ipv4.ip_forward=1Now we need to create script to enable postrouting on iptables for our network interface. First lets find out name of the network device by running ifconfig.
pi@RPi:~ $ ifconfig
enxb827eb50aa20: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.1.3 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::6c6f:d912:7a91:4e76 prefixlen 64 scopeid 0x20<link>
ether b8:27:eb:50:aa:20 txqueuelen 1000 (Ethernet)
RX packets 355432 bytes 83865639 (79.9 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 771845 bytes 223414204 (213.0 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0After we know the name we can create script that will be executed on reboot. I created mine on /root/iptables.sh after editing the file make it executable by running chmod +x /root/iptables.sh
#!/bin/sh
iptables -t nat -A POSTROUTING -o enxb827eb50aa20 -j MASQUERADERun crontab -e and add script to be executed on reboot.
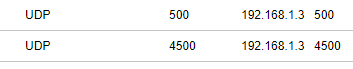
@reboot sleep 60 && /root/iptables.shRemember to forward UDP ports 500 and 4500 to your Raspberry Pi. I did this on cabins 4G router.
Now raspberry Pi device can be rebooted. Next we need to set up Lan2Lan connection on Sophos XG side.
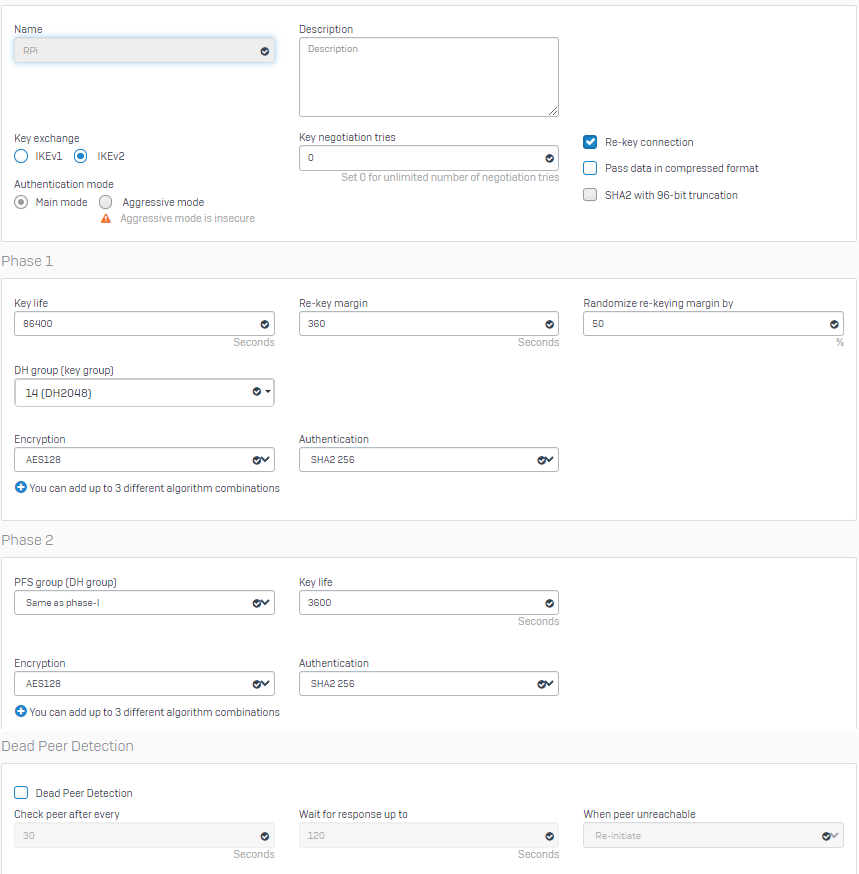
First create IPsec policy for the connection under VPN – IPsec Policies. Use same settings as we defined in /etc/ipsec.conf on Raspberry Pi. Disable Dead Peer Protection.
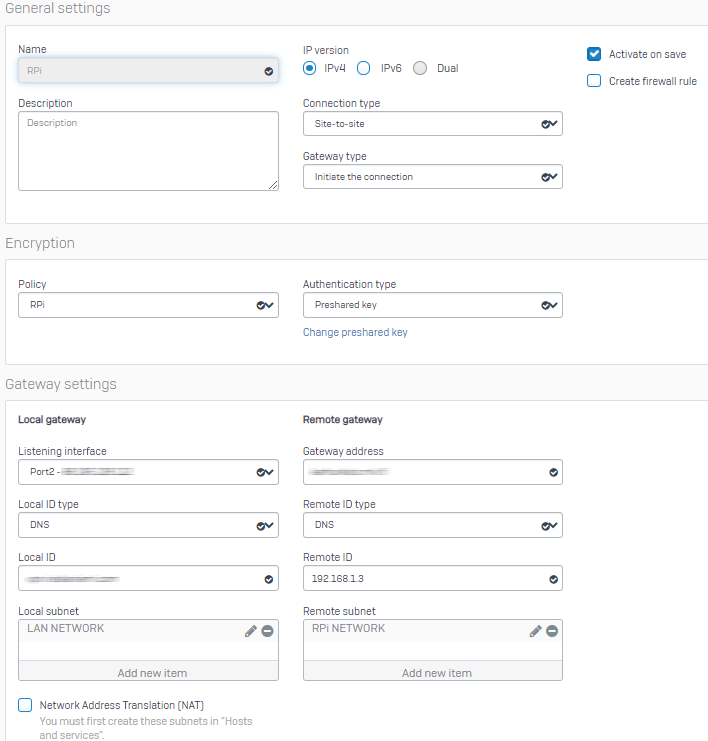
Now define new IPsec connection. Select policy we created earlier. Set local and remote ID’s to match settings defined in /etc/ipsec.conf on Raspberry Pi. Unselect “Create firewall rule”.
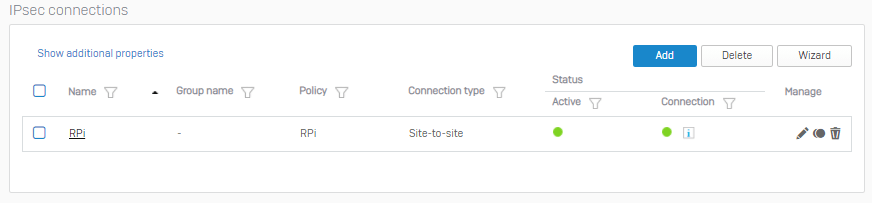
Now Tunnel should be active. You can check status from VPN page on Sophos firewall.
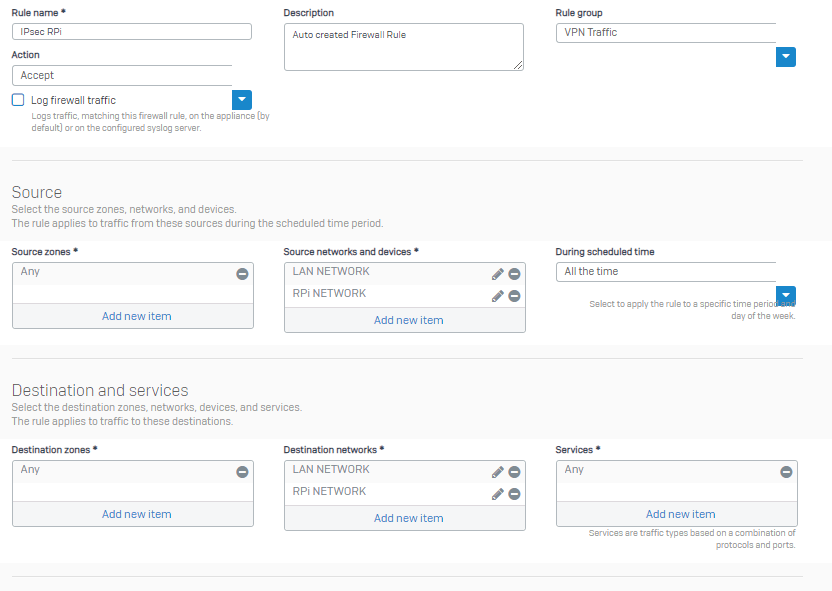
Now we need to create a firewall rule for the traffic between networks. At home simple rule like this is enough.
Quick traceroute tells traffic passes trough VPN tunnel to 4G router at cabin.
C:\Users\xxxxx>tracert 192.168.1.1
Tracing route to 192.168.1.1 over a maximum of 30 hops
1 <1 ms <1 ms <1 ms 192.168.2.1
2 36 ms 25 ms 25 ms 192.168.1.3
3 34 ms 30 ms 32 ms 192.168.1.1
Trace complete.
C:\Users\xxxxx>
Hi Kimmo,
very good post! Thanks for it!
A question about gateway settings: obfuscated gateway address must be a public ip/fqdn address or it may be a natted ip?
This is important in my case, because my LTE ISP give me only a natted ip, not a public ip.
Many thanks
lb
You need to set gateway type on Sophos side to Respond only for gateway address use 0.0.0.0 or *
If you are using IPsec client VPN then this set up will cause some problems. As they will try to connect using this L2L profile…