How to use Azure MFA With Sophos XG Firewall

With version 18 Sophos brings changes to RADIUS settings on XG Firewall. We now have possibility to set timeout for authentication and this allows us to use Azure MFA for 2-factor authentication.
Here is few simple steps how to enable this on network policy server and on XG Firewall.
If you do not have MFA enabled for your Office 365/Azure AD account you can enable it trough following link https://aka.ms/mfasetup or use conditional access policy to enforce MFA for user accounts.
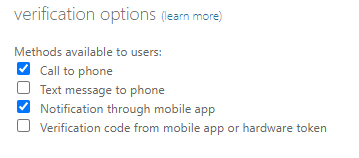
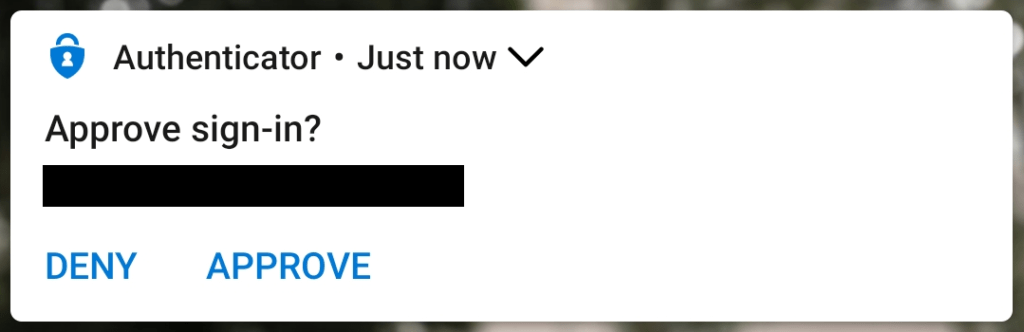
Only push message trough Microsoft Authenticator App or phone call can be used for 2-factor authentication with SSL VPN/Sophos Connect. To prevent users for selecting any other possible multi-factor authentication method you should disable verification options that are not supported.
To enable or disable verification methods, complete the following steps:
- In the Azure portal, select Azure Active Directory, then select Users.
- Select Multi-Factor Authentication.
- From Multi-Factor Authentication, select service settings.
- Unselect Text message to phone and Verification code from mobile app or hardware token
- Click Save.
Azure AD Premium P1 license should be enabled on all users using Azure MFA trough RADIUS extension. For more information refer to https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-mfa-licensing
Also remind that Network policy server with Azure MFA extension redirects all requests to Azure. Server cannot be used for any other kind of authentication (I.e. 802.1x) after enabling extension.
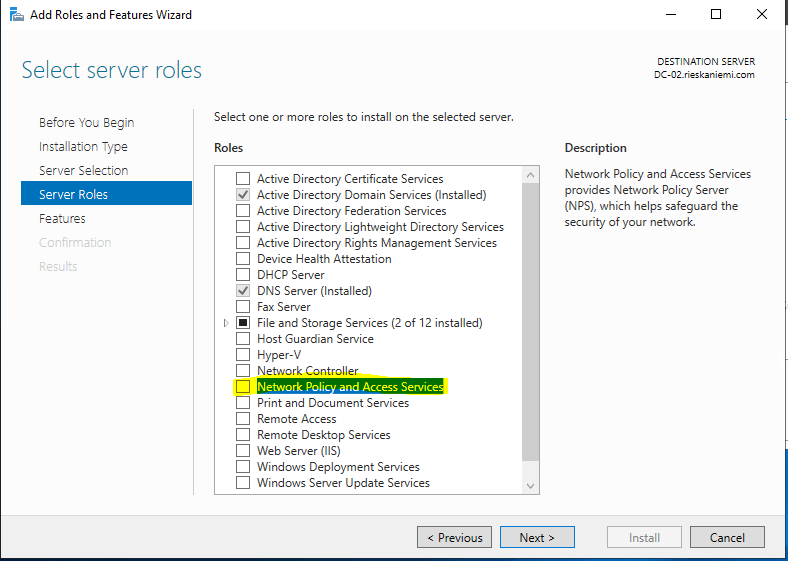
1. Install Network Policy Server role on Windows server. I installed mine on my LAB Domain Controllers.
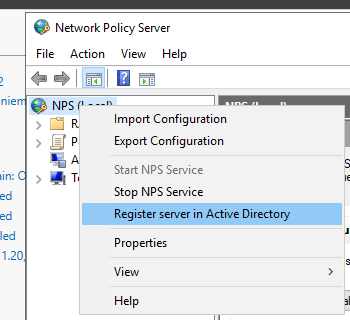
2. Install Azure MFA extension and configure it. Follow guide from Microsoft to enable it.
Download:
https://www.microsoft.com/en-us/download/details.aspx?id=54688
Guide:
https://docs.microsoft.com/bs-latn-ba/azure/active-directory/authentication/howto-mfa-nps-extension
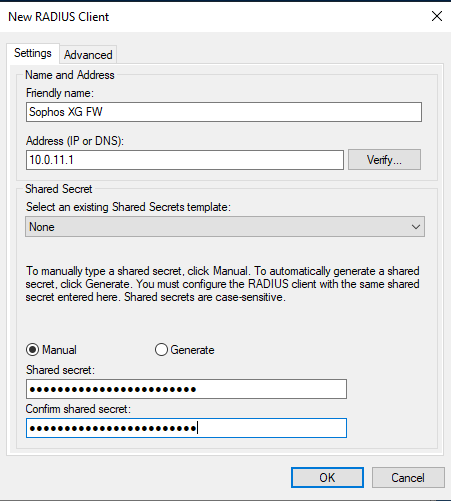
3. Create new RADIUS client with IP address of the Sophos XG Firewall.
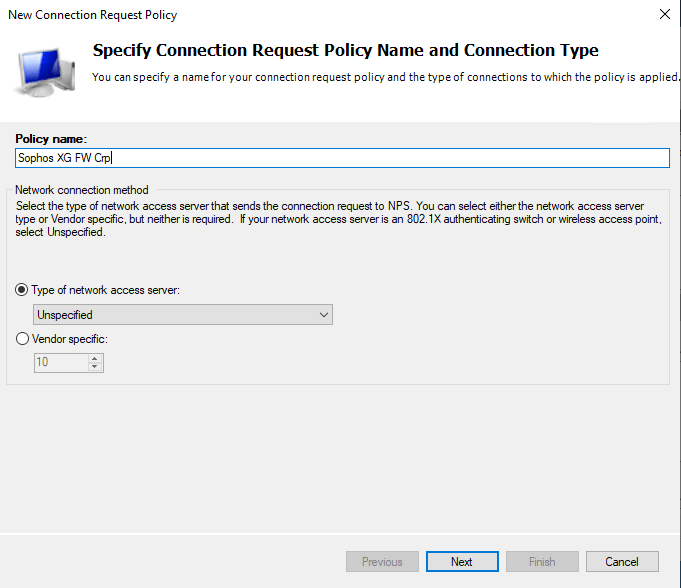
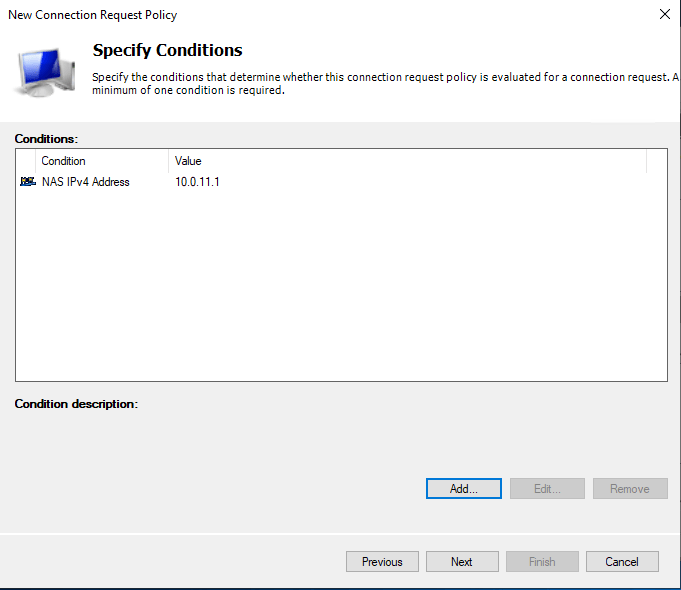
4. Create new Connection request policy.
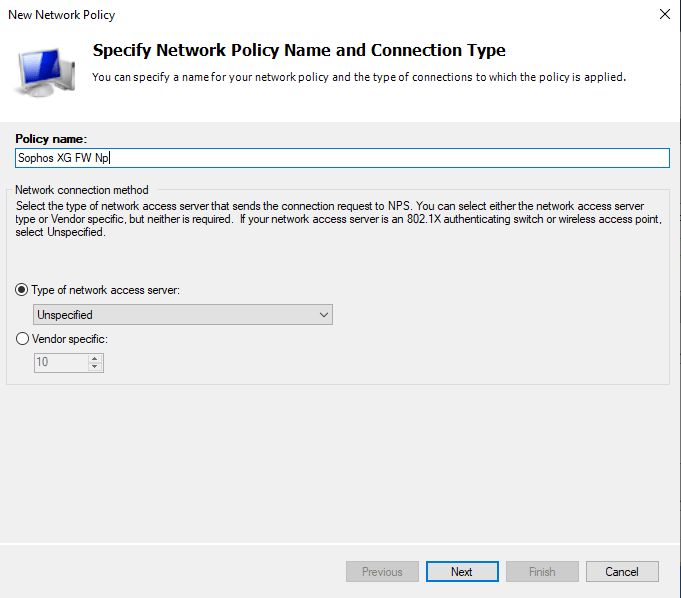
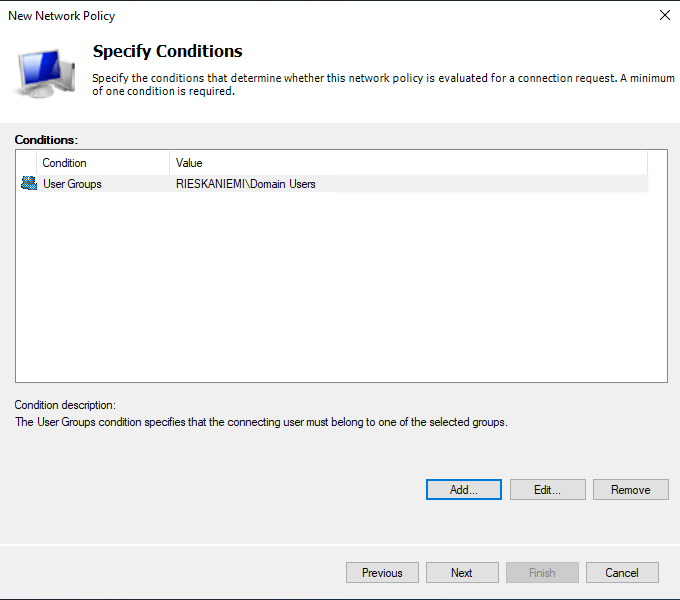
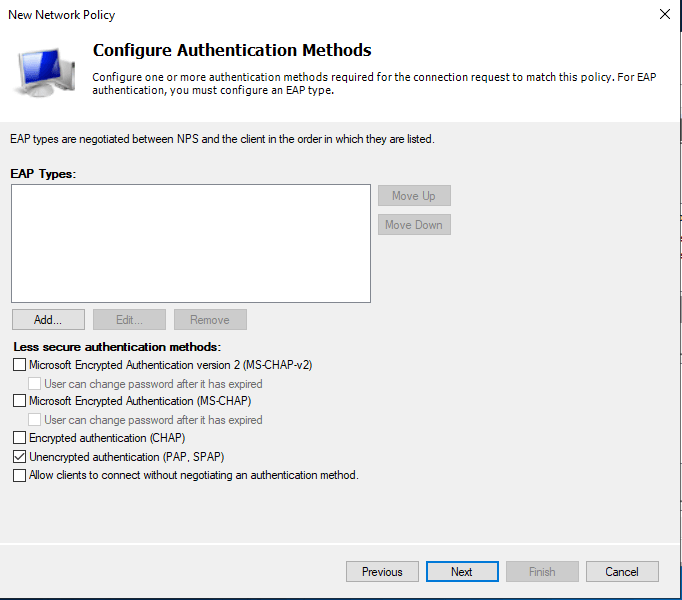
5. Create new Network Policy
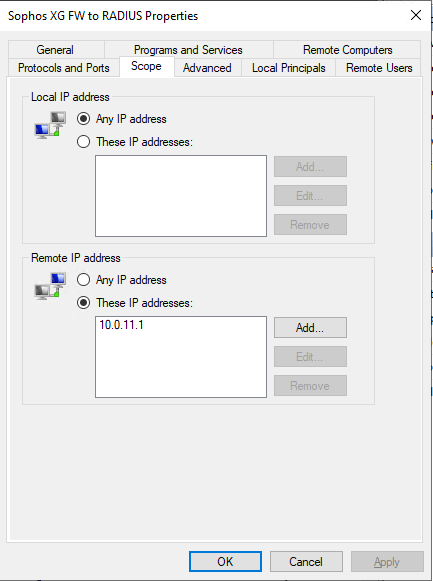
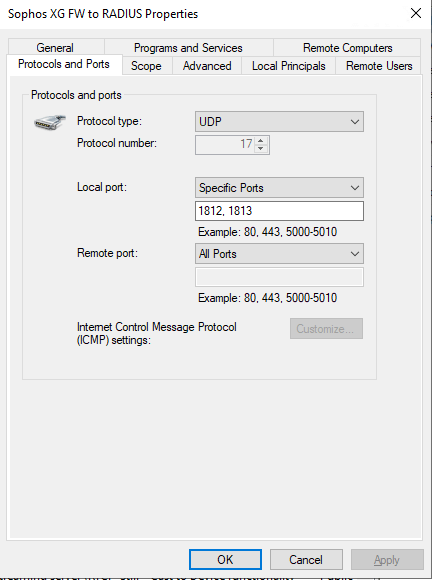
6. Create firewall rule on RADIUS Server to allow connections from Firewall.
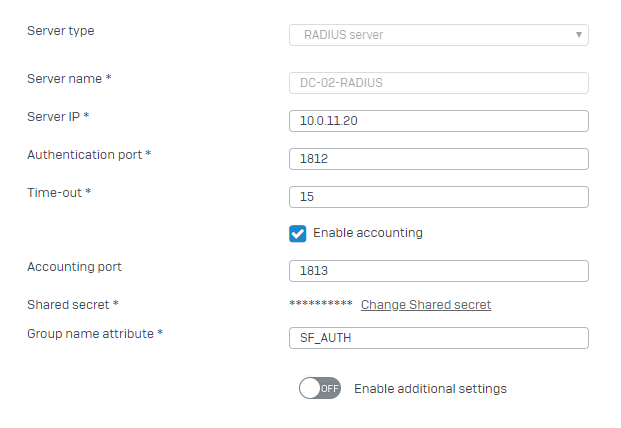
7. Add authentication server in Sophos XG Firewall.
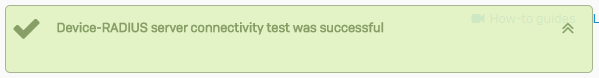
8. Test authentication trough RADIUS.
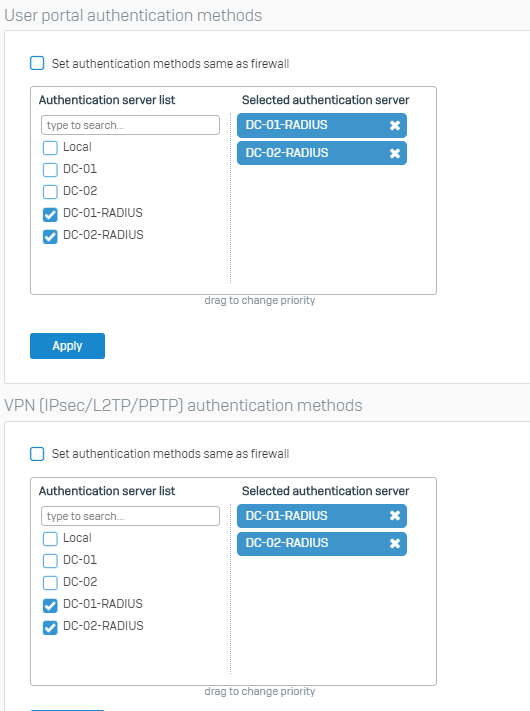
9. Select where you want to use RADIUS as authentication back-end.
Cool. This really helped me.
Thanks to you I have now MFA enabled on vpn and userportal. How cool is that??
Thank you. Tested and working perfectly. No need for MFA tokens anymore
Hello
does it work also with SMS otp?
Thanks
Alberto
Hi,
Unfortunately no as Sophos XG’s VPN client does not support this. In user portal it will work.
Push message or phone call work when using VPN.
Why do you say that the server cannot then be used for other types of RADIUS Auth such as 802.1x? Are you saying that if my NPS is already doing WPA2 Enterprise 802.1x there will be an issue? Thank you!
After installing Azure NPS extension server will forward all requests to azure MFA servers in the cloud. So NPS has to be dedicated for this use only.
Great article – thank you for sharing.
So, in your example, you could setup a 3rd NPS server (with no Azure NPS extension installed) on the domain to take care of other RADIUS client needs, such as 802.1x?
Hi, Yes this is how I have done it in the past.
For anyone that seems to have tried everything and is STILL getting the “NPS Extension for Azure MFA only performs Secondary Auth for Radius requests in AccessAccept State. Request received for User username with response state AccessReject, ignoring request.” error in event viewer, I have the fix.
You have to right-click on your network policy (named “Sophos XG FW Np” if you’re following this guide) and click “Move Up” until its processing order is #1. I just wasted a few hours trying to debug this with several dead end/incorrect errors when that is all that was preventing the auth.
Good point. On clean installstions policy should however be created with processing order 1.
Is there any way to enter the 6 digit code instead of getting a pop up? Sometimes our users don’t have cell service but need to get on VPN on their laptop.
Not with Azure MFA. For token based second factor I advice to use built in MFA from XG Firewall.
Been using it a lot with hardware and software tokens (Sophos, Google or Microsoft authenticator App). Any SHA1 hardware token will work. These are the ones I prefer: https://www.microcosm.co.uk/order/product.php?ProductID=372
Can confirm this!
Thanks for your guide and your hard work!
Regards
Martin
second thought, let your user go here:
aka.ms/mfasetup
They can change to get the code and not the app pop’up, just tested this 🙂
It all comes down to Access-Challenge response (to fill in code received trough app or SMS) not being sent back to the client as sophos VPN clients (or OpenVPN) does not support this. It will work on userportal only.
Thank you for this information. I were hitting my head against the wall with this. I can confirm only push message and call is supported indeed.
I would also want to thank you for this information.