802.1x authentication with Unifi controller and Ubiquiti access points
Ubiquiti seems to be common hardware around homelab users on reddit.
I also decided to go with Ubiquiti some years ago as I were interested on the enterprise grade hardware and software they offer for marginal price compared to big vendors like HP, Ruckus, Cisco Meraki etc…
I have also used Ubiquiti on customer installations to provide reliable and cost effective wireless network infrastructure.
As I already do have PKI infrastructure set up on my lab I decided to make one SSID available to test workstations and use certificate based authentication.
This guide assumes you already have computer and user certificates enrolled.
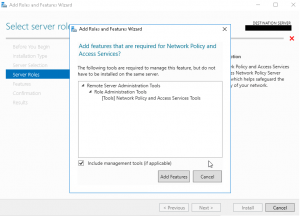
Let’s start with network policy server role installation for RADIUS clients.
After NPS role is installed we can continue setting up RADIUS. You should already have computer certificate enrolled to server where you installed NPS role. I am using computer certificate auto enrollment for all my servers and workstations on LAB domain, and have this policy defined in default domain policy.
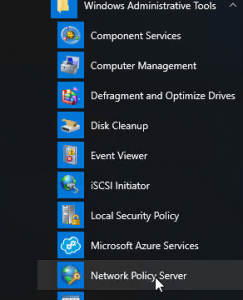
Start Network Policy Server management under Windows Administrative Tools
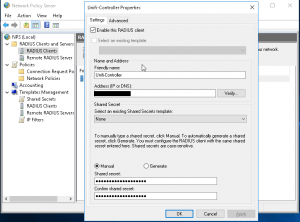
We start by adding new RADIUS client to the network policy server.
I named this Unifi-Controller. Use IP-Address of the controller.
Type in a shared secret, we will use this later when we setup Unifi controller.
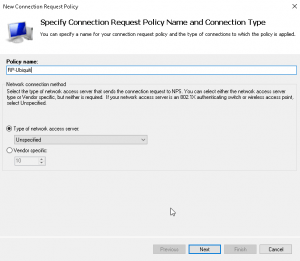
Then let’s create new connection request policy. I named mine RP-Ubiquiti.
Leave type as Unspecified and click next.
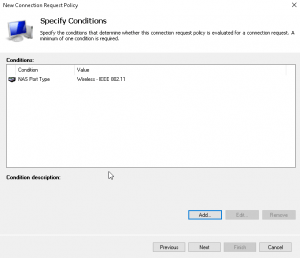
Under conditions add new condition as NAS Port Type and set value as Wireless IEEE 802.11
Leave rest of the settings as default.
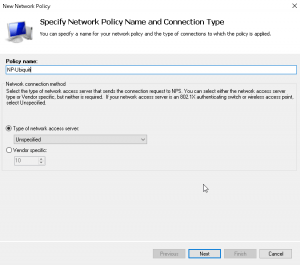
Now let’s create network policy setting. Again I named mine as NP-Ubiquiti.
Leave type as unspecified and click next.
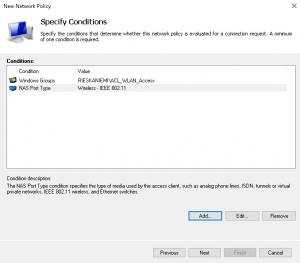
Next we will add some conditions.
I am using windows group to define users who should have access to WLAN.
Also add NAS Port Type Wireless IEEE 802.11 as with connection request policy
On next page leave specify access permission as access granted.
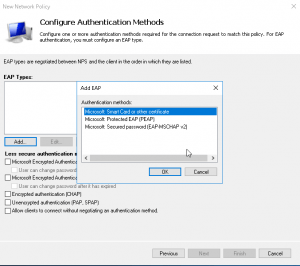
Under authentication methods clear all settings and on EAP types click on Add
Select Microsoft smart card or other certificate
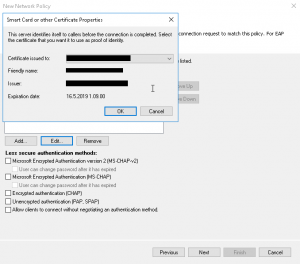
Select EAP type we just selected and click on edit.
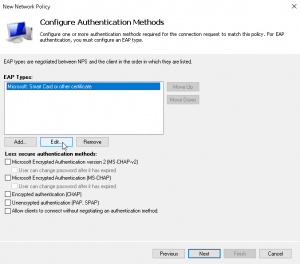
Select computer certificate that has been enrolled to the NPS machine and click on OK.
That’s it for the network policy server. Now let’s change some settings on Unifi controller.
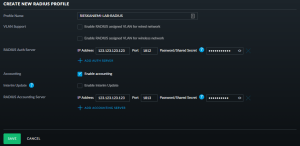
Log-in to Unifi controller and create new RADIUS profile under profiles.
Fill-in policy server address and same shared secret we used on client settings.
Select enable accounting and fill-in details as you did for auth server.
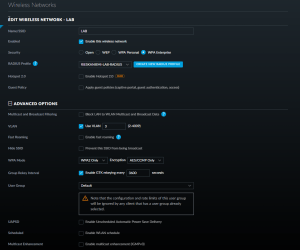
Next let’s create new Wireless network or edit existing one.
Select WPA Enterprise as security type and for radius profile select profile we created on last step.
Thats it for Unifi. Now let’s try to connect with user certificate.
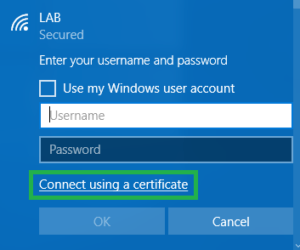
On workstation select the network and instead of using username/password click on Connect using a certificate.
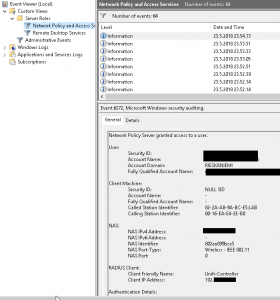
On network policy server we can see user successfully granted access to network.
Hi,
Did it mean we have to setup AD first? Or we have to had AD first?
Thanks
Yes you need to have AD set up first and also MS certificate services set up.
hello,
what is with private phones? they dont trust my internal certificate. so how to get them into the system without a certificate warning?
thank!
Hi,
You would need to use MDM to deploy certificates to mobile devices.
As connecting phones are private I strongly recommend creating separate guest network with own PSK secured SSID.
are you using user or computer-based certs?
Depends on use case. On shared computers computer certificates and on assigned devices I prefer user certificates. Mostly it has been user certs. Devices are normally connected to docks and wired connection and connect automatically with user certificate to WiFi when in meeting rooms etc.
Hello,
Just wondered if it would make sense not to auto enroll certificates to clients ( so that we can have control over which computers will be able to connect ) to prevent unauthorized access even user credentials are exposed? ( ok there is a trade off of manual certification at client computers but in case we ignore that )
Hi,
Sure. Manual certificate enrollment is a bit of a hassle. But what you could do is create group policy for certificate enrollment and filter it using security group with allowed computers inside.
https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-firewall/assign-security-group-filters-to-the-gpo
Or you could use a security group in RADIUS policies to prevent access to wlan. This would be more flexible solution.